Premium Only Content
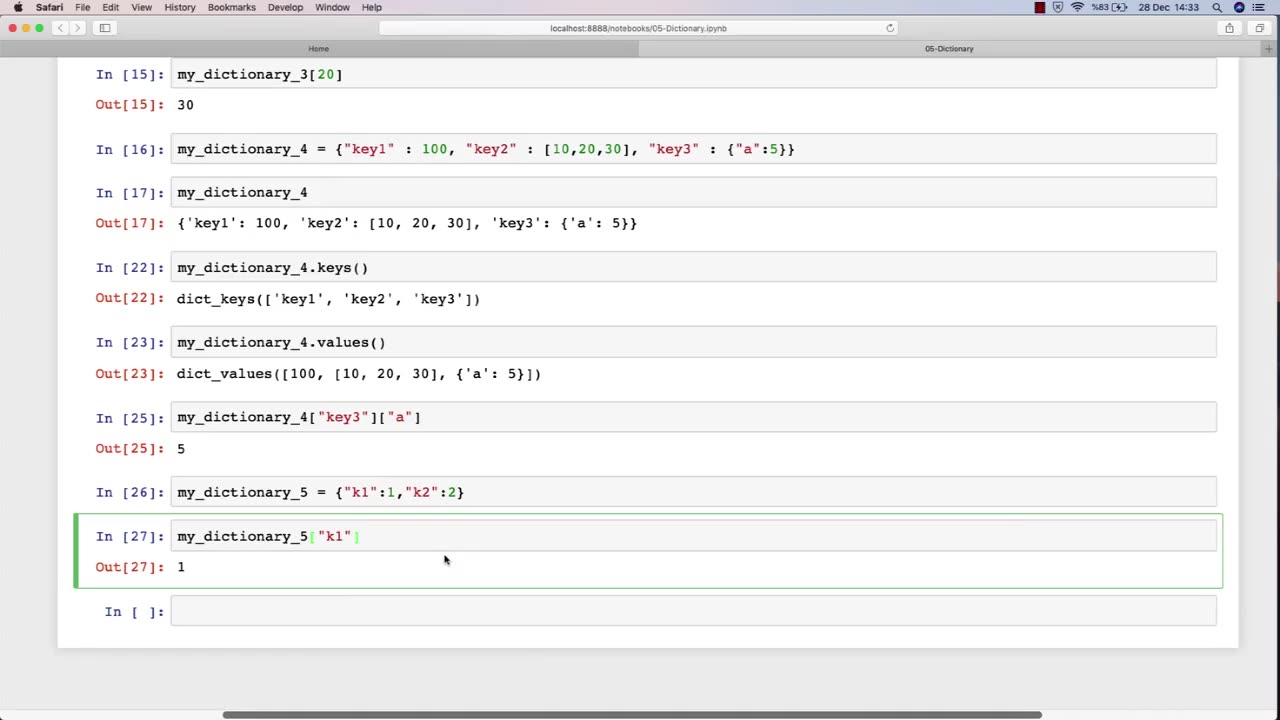
Chapter-27, PEC-10 | Dictionary | #ethicalhacking #hacking #education #growthhacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking
Dictionary: "Ethical Hacking Terminology"
Description: The ethical hacking terminology dictionary is a collection of technical terms and jargon commonly used in the field of ethical hacking. These terms are used to describe various tools, techniques, and methodologies used by ethical hackers to identify and address security vulnerabilities in computer systems and networks. The following is a list of some of the common terms that may be included in an ethical hacking course:
Exploit - A piece of software or code that takes advantage of a vulnerability in a computer system or network.
Payload - The part of an exploit that performs a malicious action, such as stealing data or taking control of a system.
Vulnerability - A weakness in a computer system or network that can be exploited by attackers to gain unauthorized access or perform malicious actions.
Penetration Testing - The process of identifying and exploiting vulnerabilities in a computer system or network to assess its security posture.
Social Engineering - The use of psychological manipulation to trick people into revealing sensitive information or performing actions that are harmful to their organization.
Malware - Software that is designed to perform malicious actions, such as stealing data or taking control of a system.
Brute Force Attack - A method of guessing a password by trying every possible combination until the correct one is found.
Rootkit - A type of malware that hides its presence on a system and gives an attacker privileged access to the system.
Denial of Service (DoS) Attack - A type of attack that floods a network or system with traffic to make it unavailable to legitimate users.
Firewall - A security measure that monitors and controls incoming and outgoing network traffic to prevent unauthorized access.
The ethical hacking terminology dictionary is an important resource for students to learn and understand the technical terms and jargon used in the field of ethical hacking. By mastering these terms, students can communicate effectively with other professionals in the field and better understand the technical aspects of ethical hacking.
-
 DVR
DVR
DLDAfterDark
4 hours agoGun Talk LIVE! Thursday At The Armory! Feat. Josh of BDG&G & DLD
1.74K1 -
 2:50:16
2:50:16
TimcastIRL
5 hours agoSupreme Court May OVERTURN Gay Marriage, SCOTUS Hearing Set For TOMORROW | Timcast IRL
203K110 -
 4:06:47
4:06:47
Barry Cunningham
6 hours agoBREAKING NEWS: PRESIDENT TRUMP HOSTS A STATE DINNER | FOX NATION PATRIOT AWARDS!
85.3K58 -
 DVR
DVR
Alex Zedra
4 hours agoLIVE! New Game | The See Us
18.2K1 -
 1:56:30
1:56:30
ThisIsDeLaCruz
4 hours ago $0.03 earnedOn The Road With Pantera
19.3K1 -
 LIVE
LIVE
meleegames
3 hours agoMelee Madness Podcast #58 - They Changed What ‘It’ Was & It’ll Happen to You
81 watching -
 2:32:46
2:32:46
megimu32
5 hours agoOn The Subject: Why K-Pop Demon Hunters Feels Like 90s Disney Again
15K9 -
 1:38:28
1:38:28
Glenn Greenwald
8 hours agoThe Fraudulent GOP War Against Tucker and Nick Fuentes; Dick Cheney: Hero of the Resistance; Lindsey Graham's Deranged RJC Comments | SYSTEM UPDATE #544
97.8K113 -
 LIVE
LIVE
ThePope_Live
3 hours agoRedsack with the boys Cheap, Jah and Nova!
456 watching -
 LIVE
LIVE
Hernandez2787
7 hours agoArc Raiders - 1st Playthrough/ Celebrating My Anniversary as Sergeant First Class in the US Army
72 watching