Premium Only Content
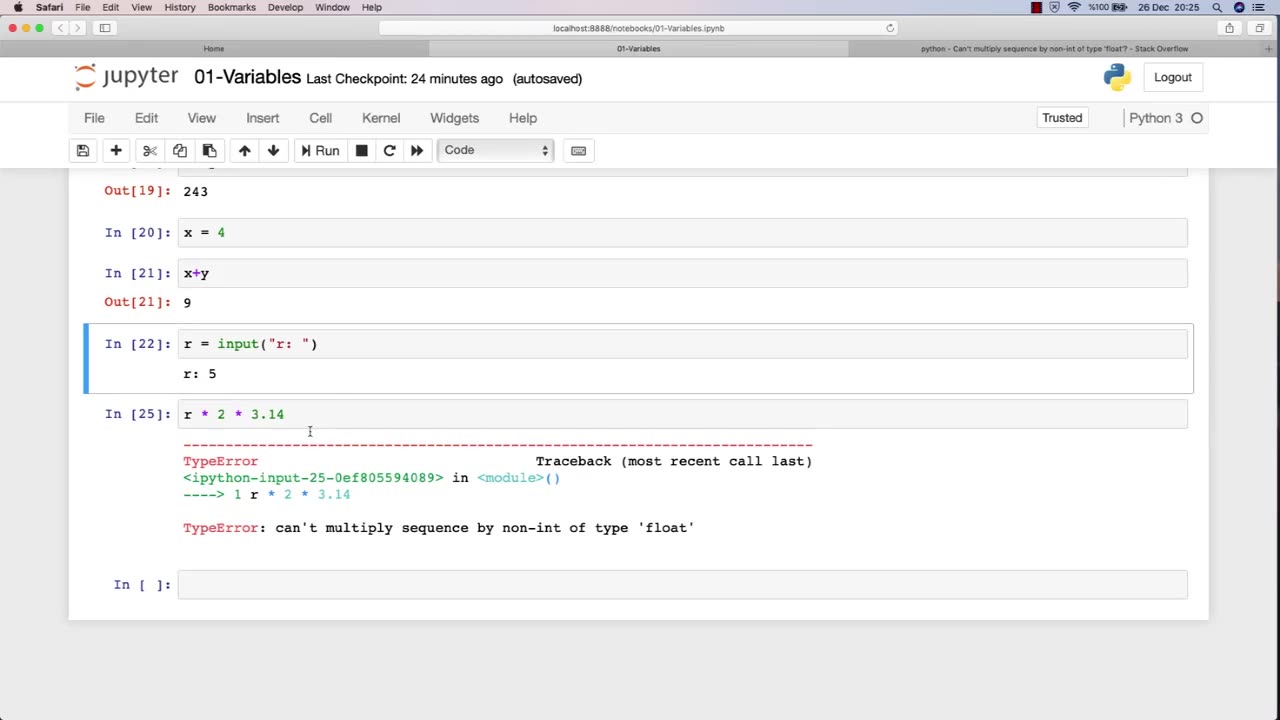
Chapter-27, LEC-3 | Variables | #rumble #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Variables are fundamental to programming, and they play a crucial role in ethical hacking. A variable is a storage location that holds a value or a reference to a value, and it can be manipulated by a program or script. In ethical hacking, variables are used to store and manipulate various types of data that are essential for carrying out attacks, testing security, and analyzing vulnerabilities.
Here are some examples of how variables are used in ethical hacking:
Target variables: These variables store information about the target system or network, such as IP addresses, domain names, and operating system versions. Ethical hackers use these variables to identify vulnerabilities and potential attack vectors.
Payload variables: These variables store the data or commands used in an attack, such as code snippets, exploit payloads, or malicious scripts. Ethical hackers use these variables to execute attacks, test security controls, and assess the effectiveness of countermeasures.
Password variables: Password variables store the passwords used to access computer systems and networks. Ethical hackers use password variables to test the strength of passwords, identify weak passwords, and crack passwords using various techniques.
Encryption variables: These variables store encryption keys, algorithms, and other information related to encryption. Ethical hackers use these variables to test the strength of encryption, identify vulnerabilities, and analyze weaknesses in encryption systems.
Environment variables: These variables store information about the system or network environment, such as system paths, environment variables, and configuration settings. Ethical hackers use these variables to analyze system configurations, identify vulnerabilities, and assess the security posture of a system or network.
Overall, variables are an essential component of ethical hacking, and a strong understanding of how to work with variables is crucial for success in this field. By effectively using variables, ethical hackers can more efficiently and effectively identify and address vulnerabilities in computer systems and networks.
-
 58:46
58:46
The Charlie Kirk Show
1 hour agoLive Reaction to Utah Prosecutors Press Conference on Charlie Kirk Assassination
146K89 -
 1:58:57
1:58:57
The Quartering
3 hours agoCharlie Kirk Assassination Appears In Court!
181K46 -
 1:05:13
1:05:13
Russell Brand
4 hours agoReporting From Tommy Robinson’s ‘Unite the Kingdom’ March - SF634
115K58 -
 LIVE
LIVE
Rallied
2 hours ago $0.31 earnedWarzone Challenges All Night
77 watching -
 55:05
55:05
Committee on House Administration
1 day agoSubcommittee on Elections Hearing:“Maintaining Election Operations in the Face of Natural Disasters”
16.1K -
 5:56
5:56
Buddy Brown
4 hours ago $3.44 earnedThis is Why Everyone's Googling September 23rd! | Buddy Brown
28.5K20 -
 58:33
58:33
Human Events Daily with Jack Posobiec
2 hours agoBreaking: Utah Prosecutors Announce Charges Against Charlie Kirk Assassin
33.1K3 -
 3:21
3:21
Michael Heaver
3 hours agoGermany’s Seismic Result Serves WARNING
21.4K4 -
 1:02:14
1:02:14
SGT Report
18 hours agoGOD'S ORDER VS. SATAN'S CHAOS -- Dr. Henry Ealy
36.7K38 -
 2:03:13
2:03:13
The Charlie Kirk Show
5 hours agoMichael Knowles, Matt Walsh, and Ben Shapiro Remember Charlie Kirk | 9.16.2025
444K455