Premium Only Content
Chapter-27, LEC-3 | Variables | #rumble #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
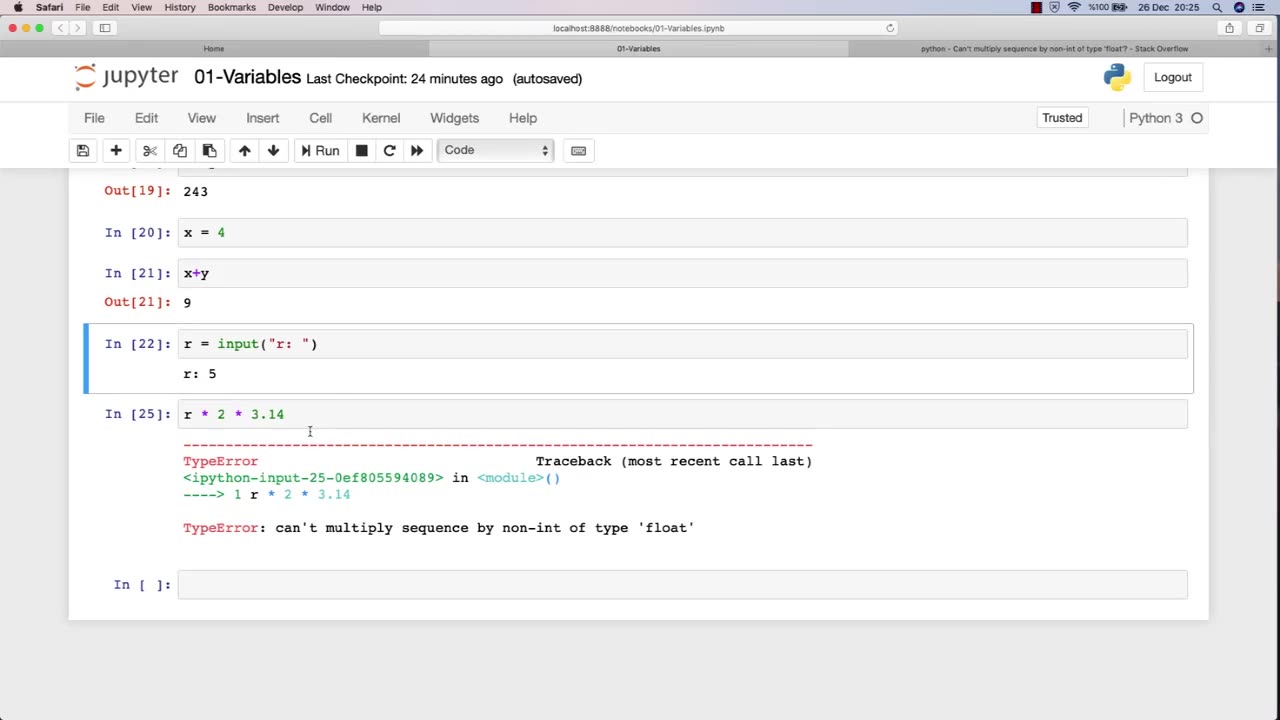
Variables are fundamental to programming, and they play a crucial role in ethical hacking. A variable is a storage location that holds a value or a reference to a value, and it can be manipulated by a program or script. In ethical hacking, variables are used to store and manipulate various types of data that are essential for carrying out attacks, testing security, and analyzing vulnerabilities.
Here are some examples of how variables are used in ethical hacking:
Target variables: These variables store information about the target system or network, such as IP addresses, domain names, and operating system versions. Ethical hackers use these variables to identify vulnerabilities and potential attack vectors.
Payload variables: These variables store the data or commands used in an attack, such as code snippets, exploit payloads, or malicious scripts. Ethical hackers use these variables to execute attacks, test security controls, and assess the effectiveness of countermeasures.
Password variables: Password variables store the passwords used to access computer systems and networks. Ethical hackers use password variables to test the strength of passwords, identify weak passwords, and crack passwords using various techniques.
Encryption variables: These variables store encryption keys, algorithms, and other information related to encryption. Ethical hackers use these variables to test the strength of encryption, identify vulnerabilities, and analyze weaknesses in encryption systems.
Environment variables: These variables store information about the system or network environment, such as system paths, environment variables, and configuration settings. Ethical hackers use these variables to analyze system configurations, identify vulnerabilities, and assess the security posture of a system or network.
Overall, variables are an essential component of ethical hacking, and a strong understanding of how to work with variables is crucial for success in this field. By effectively using variables, ethical hackers can more efficiently and effectively identify and address vulnerabilities in computer systems and networks.
-
 2:09:24
2:09:24
Inverted World Live
5 hours agoRats Have Learned to Hunt Bats | Ep. 135
25.2K5 -
 2:48:01
2:48:01
TimcastIRL
6 hours agoLIVE Election Coverage: Polling Stations SWATTED, Bomb Threats Called In | Timcast IRL
232K164 -
 3:30:07
3:30:07
Barry Cunningham
6 hours agoBREAKING NEWS: COUNTDOWN TO COMMUNISM! ELECTION RESULTS SHOW!
48.1K40 -
 2:11:28
2:11:28
DeVory Darkins
5 hours agoLIVE NOW: 2025 Election results and Exit Polls AMA
57.9K42 -
 2:34:04
2:34:04
DLDAfterDark
4 hours ago $0.05 earnedJust Another Tuesday - In Virginia - The Governor's Race & Glock Talk
21.6K2 -
 3:21:38
3:21:38
The Charlie Kirk Show
7 hours agoJUDGMENT DAY 2025: The Election Results Stream
186K78 -
 3:51:07
3:51:07
MattMorseTV
8 hours ago $0.77 earned🔴Election Day LIVE COVERAGE.🔴
91.2K47 -
 1:16:51
1:16:51
Flyover Conservatives
1 day agoSHOCKING DATA REVEALS: Young Voters Are Done With the Old GOP - Mark Mitchell, Rasmussen Reports | FOC Show
37.1K16 -
 1:15:28
1:15:28
Sarah Westall
7 hours agoGrooming is Protected and Encouraged by the System – Michelle Peterson and Mike Adamovich
32K10 -
 4:00:13
4:00:13
Akademiks
5 hours agoKendrick tries to Flip the Bots on DRAKE? WHo Beats Jay z in a verzuz. Blueface finally free!
36.5K7