Premium Only Content
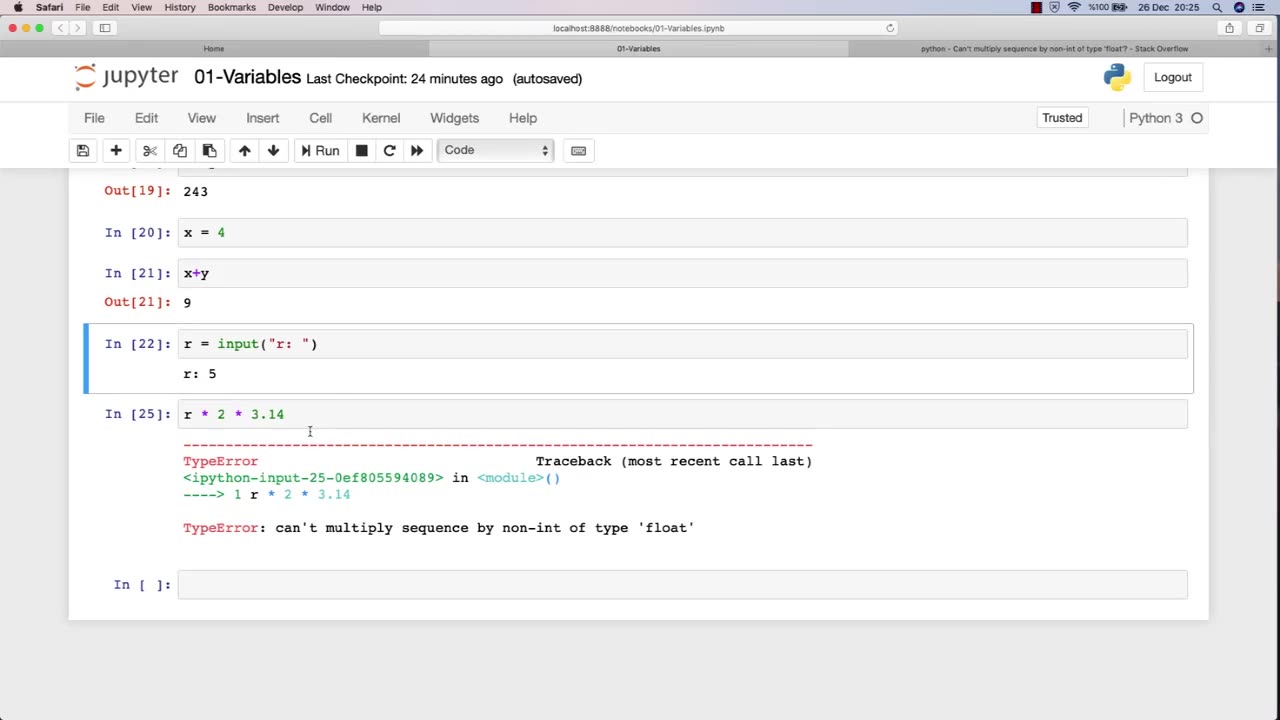
Chapter-27, LEC-3 | Variables | #rumble #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
Variables are fundamental to programming, and they play a crucial role in ethical hacking. A variable is a storage location that holds a value or a reference to a value, and it can be manipulated by a program or script. In ethical hacking, variables are used to store and manipulate various types of data that are essential for carrying out attacks, testing security, and analyzing vulnerabilities.
Here are some examples of how variables are used in ethical hacking:
Target variables: These variables store information about the target system or network, such as IP addresses, domain names, and operating system versions. Ethical hackers use these variables to identify vulnerabilities and potential attack vectors.
Payload variables: These variables store the data or commands used in an attack, such as code snippets, exploit payloads, or malicious scripts. Ethical hackers use these variables to execute attacks, test security controls, and assess the effectiveness of countermeasures.
Password variables: Password variables store the passwords used to access computer systems and networks. Ethical hackers use password variables to test the strength of passwords, identify weak passwords, and crack passwords using various techniques.
Encryption variables: These variables store encryption keys, algorithms, and other information related to encryption. Ethical hackers use these variables to test the strength of encryption, identify vulnerabilities, and analyze weaknesses in encryption systems.
Environment variables: These variables store information about the system or network environment, such as system paths, environment variables, and configuration settings. Ethical hackers use these variables to analyze system configurations, identify vulnerabilities, and assess the security posture of a system or network.
Overall, variables are an essential component of ethical hacking, and a strong understanding of how to work with variables is crucial for success in this field. By effectively using variables, ethical hackers can more efficiently and effectively identify and address vulnerabilities in computer systems and networks.
-
 2:50:16
2:50:16
TimcastIRL
5 hours agoSupreme Court May OVERTURN Gay Marriage, SCOTUS Hearing Set For TOMORROW | Timcast IRL
203K110 -
 4:06:47
4:06:47
Barry Cunningham
6 hours agoBREAKING NEWS: PRESIDENT TRUMP HOSTS A STATE DINNER | FOX NATION PATRIOT AWARDS!
85.3K58 -
 DVR
DVR
Alex Zedra
4 hours agoLIVE! New Game | The See Us
18.2K1 -
 1:56:30
1:56:30
ThisIsDeLaCruz
4 hours ago $0.03 earnedOn The Road With Pantera
19.3K1 -
 LIVE
LIVE
meleegames
3 hours agoMelee Madness Podcast #58 - They Changed What ‘It’ Was & It’ll Happen to You
81 watching -
 2:32:46
2:32:46
megimu32
5 hours agoOn The Subject: Why K-Pop Demon Hunters Feels Like 90s Disney Again
15K9 -
 1:38:28
1:38:28
Glenn Greenwald
8 hours agoThe Fraudulent GOP War Against Tucker and Nick Fuentes; Dick Cheney: Hero of the Resistance; Lindsey Graham's Deranged RJC Comments | SYSTEM UPDATE #544
97.8K113 -
 LIVE
LIVE
ThePope_Live
3 hours agoRedsack with the boys Cheap, Jah and Nova!
460 watching -
 LIVE
LIVE
Hernandez2787
7 hours agoArc Raiders - 1st Playthrough/ Celebrating My Anniversary as Sergeant First Class in the US Army
70 watching -
 48:42
48:42
Donald Trump Jr.
8 hours agoCommunism vs Common Sense, What's Next for NYC? | TRIGGERED Ep.289
141K279