Premium Only Content
Chapter-27, LEC-3 | Variables | #rumble #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
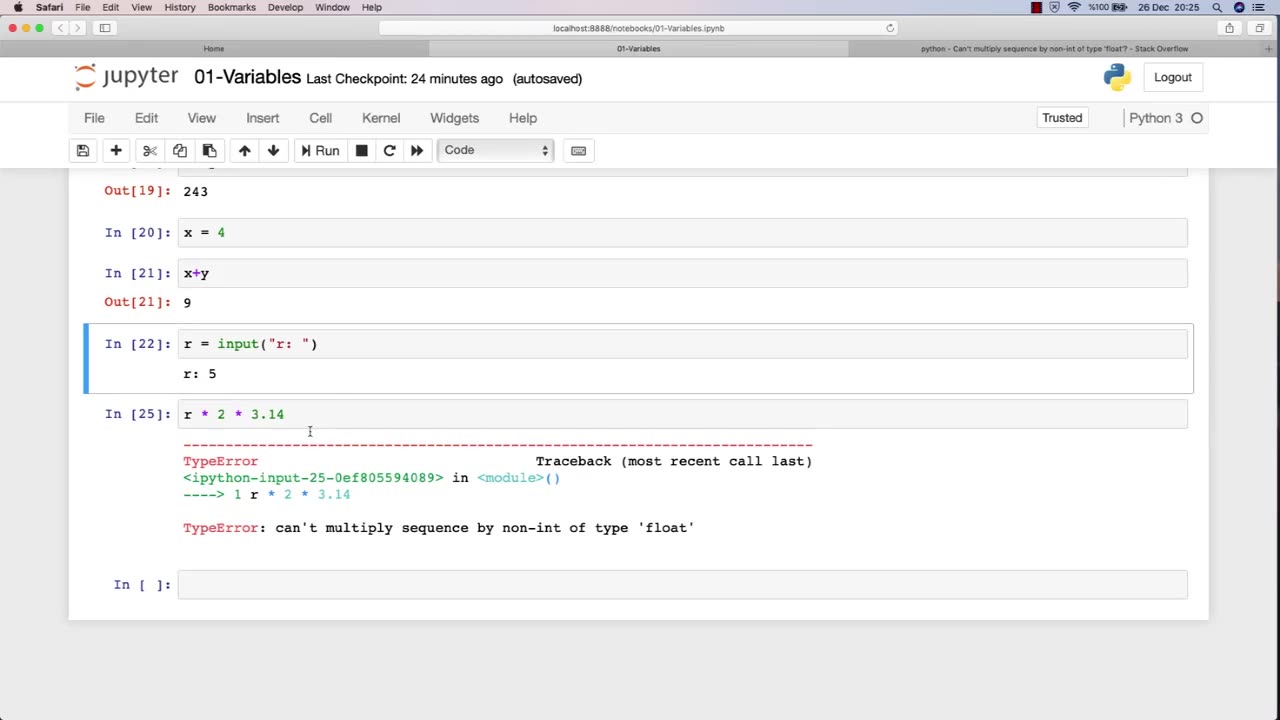
Variables are fundamental to programming, and they play a crucial role in ethical hacking. A variable is a storage location that holds a value or a reference to a value, and it can be manipulated by a program or script. In ethical hacking, variables are used to store and manipulate various types of data that are essential for carrying out attacks, testing security, and analyzing vulnerabilities.
Here are some examples of how variables are used in ethical hacking:
Target variables: These variables store information about the target system or network, such as IP addresses, domain names, and operating system versions. Ethical hackers use these variables to identify vulnerabilities and potential attack vectors.
Payload variables: These variables store the data or commands used in an attack, such as code snippets, exploit payloads, or malicious scripts. Ethical hackers use these variables to execute attacks, test security controls, and assess the effectiveness of countermeasures.
Password variables: Password variables store the passwords used to access computer systems and networks. Ethical hackers use password variables to test the strength of passwords, identify weak passwords, and crack passwords using various techniques.
Encryption variables: These variables store encryption keys, algorithms, and other information related to encryption. Ethical hackers use these variables to test the strength of encryption, identify vulnerabilities, and analyze weaknesses in encryption systems.
Environment variables: These variables store information about the system or network environment, such as system paths, environment variables, and configuration settings. Ethical hackers use these variables to analyze system configurations, identify vulnerabilities, and assess the security posture of a system or network.
Overall, variables are an essential component of ethical hacking, and a strong understanding of how to work with variables is crucial for success in this field. By effectively using variables, ethical hackers can more efficiently and effectively identify and address vulnerabilities in computer systems and networks.
-
 LIVE
LIVE
The Jimmy Dore Show
52 minutes agoTrump Threatens to INVADE Nigeria! Kash Patel CRASHES OUT Over Jet Use Criticism!
4,506 watching -
 DVR
DVR
Kim Iversen
2 hours agoTrump’s Nigeria Threat Isn’t About Christians — It’s About China
63.3K49 -
 LIVE
LIVE
Sean Unpaved
1 hour agoDodgers Dynasty Rolls On, NFL Chaos Reigns, & MNF Showdown Countdown
94 watching -
 1:35:56
1:35:56
Redacted News
3 hours agoA MAGA Civil War has just begun, Christians slaughtered in Nigeria, Charlie Kirk's audiit | Redacted
101K123 -
 LIVE
LIVE
Dr Disrespect
8 hours ago🔴LIVE - DR DISRESPECT - ARC RAIDERS - FULL SEND INTO THE RED
1,537 watching -
 26:34
26:34
Stephen Gardner
3 hours ago🔥Elon EXPOSES The Exact Blueprint Dems use to CHEAT on Joe Rogan!!
30.1K85 -
 51:10
51:10
Dad Saves America
7 hours ago $0.36 earnedMask Off Mamdani: NYC’s Socialist “Savior” Is Another Spoiled Aristocrat
14.8K5 -
 6:14
6:14
Buddy Brown
8 hours ago $1.61 earnedLaw Enforcement Caught SNOOPING on PRIVATE LAND! | Buddy Brown
15.2K23 -
 16:21
16:21
Real Estate
1 month ago $0.28 earnedIt’s Not Just You..NO ONE CAN AFFORD KIDS ANYMORE
15.2K6 -
 LIVE
LIVE
LFA TV
1 day agoLIVE & BREAKING NEWS! | MONDAY 11/3/25
878 watching