Premium Only Content
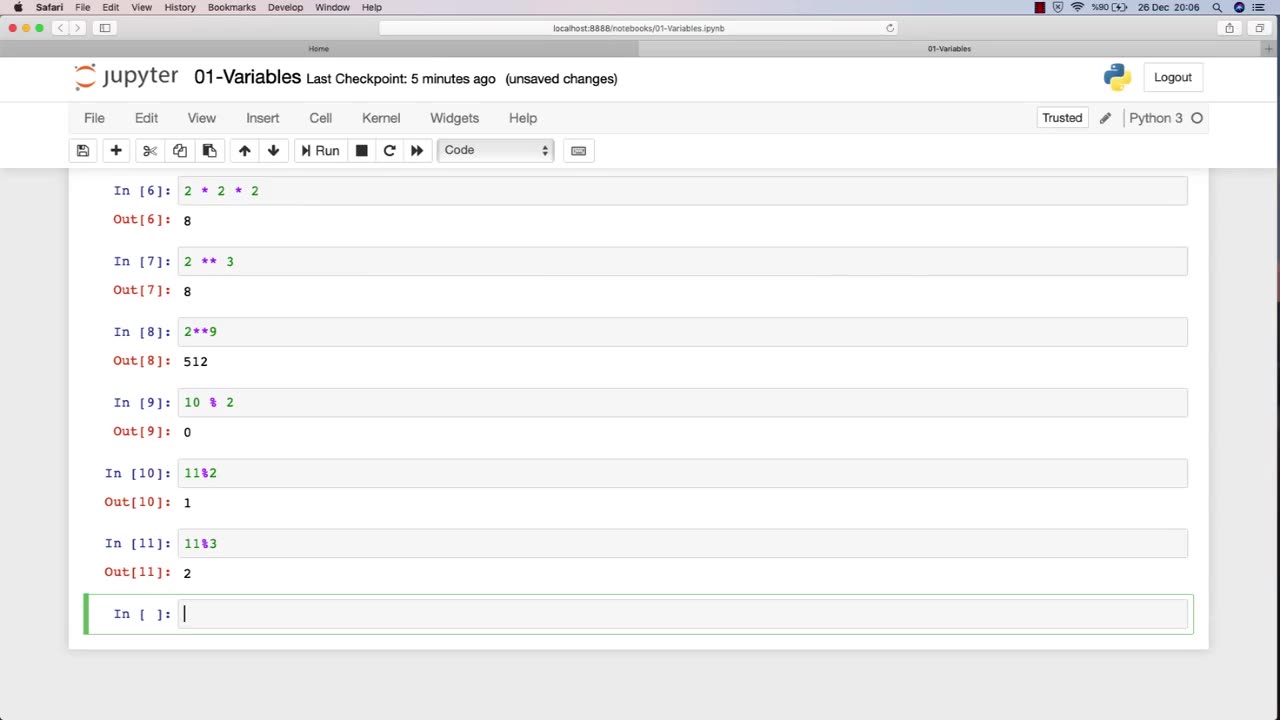
Chapter-27, LEC-2 | Numbers | #ethicalhacking #hacking #education #cybersport #cybersecurity
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram
Ethical hacking is a field that involves the use of various techniques and tools to identify and address vulnerabilities in computer systems and networks. Numbers play a critical role in ethical hacking, and understanding how to work with numbers is essential for success in this field.
Here are some examples of how numbers are used in ethical hacking:
IP Addresses: IP addresses are used to identify network devices and are essential for ethical hackers to understand. Ethical hackers use IP addresses to scan for open ports, identify potential vulnerabilities, and carry out attacks.
Ports: Ports are used to establish connections between devices on a network. Ethical hackers use knowledge of port numbers to scan for vulnerabilities, carry out attacks, and test the security of a network.
Passwords: Passwords are often used to protect sensitive information in computer systems and networks. Ethical hackers use various techniques to crack passwords, such as brute-force attacks, dictionary attacks, and rainbow table attacks.
Encryption: Encryption is the process of converting data into a secure format that cannot be read by unauthorized parties. Ethical hackers use their understanding of encryption algorithms and techniques to identify vulnerabilities and weaknesses in encryption systems.
Binary and hexadecimal: Binary and hexadecimal are number systems used in computing. Ethical hackers use their understanding of these number systems to analyze and manipulate data at the low-level, such as reverse engineering software or discovering vulnerabilities in firmware.
Overall, a strong understanding of numbers is essential for success in ethical hacking. By understanding how numbers are used in this field, ethical hackers can more effectively identify and address vulnerabilities in computer systems and networks.
-
 16:44
16:44
Russell Brand
2 hours agoAmerica’s Hidden Royalty
14.9K15 -
 2:05:29
2:05:29
The Quartering
4 hours agoEscape From New York, Harvard Bombers Caught, Trump DEFIES Court On SNAP, Bomb Threat On Plane!
153K85 -
 LIVE
LIVE
StoneMountain64
4 hours agoBattlefield REDSEC leveling guns for attachments
181 watching -
 16:30
16:30
Clintonjaws
18 hours ago $8.35 earned'The View's' Producer Stops Show & Forces Whoopie To Correct Lie
32.5K16 -
 10:51
10:51
Scammer Payback
2 hours agoScammer's Meltdown after He's Been Hacked
3.72K3 -
 LIVE
LIVE
LFA TV
20 hours agoLIVE & BREAKING NEWS! | TUESDAY 11/4/25
1,353 watching -
 LIVE
LIVE
freecastle
5 hours agoTAKE UP YOUR CROSS- INTEGRITY of the upright GUIDES them, CROOKEDNESS of the treacherous DESTROYS!
126 watching -
 2:04:16
2:04:16
Pop Culture Crisis
3 hours agoCoca-Cola's WAR ON CHRISTMAS, Movie Press Tour CRINGE, Gen Z HATES Gen Z | Ep, 949
28.5K4 -
 1:10:24
1:10:24
Steve-O's Wild Ride! Podcast
5 days ago $0.98 earnedMatt McCusker Makes Steve-O Nervous | Wild Ride #272
24.9K2 -
 17:09
17:09
Bearing
10 hours agoHasan Goes NUCLEAR On Chat ☢️ ROASTED By JD Vance Over Dog Allegations 🚨
26.7K33