Premium Only Content
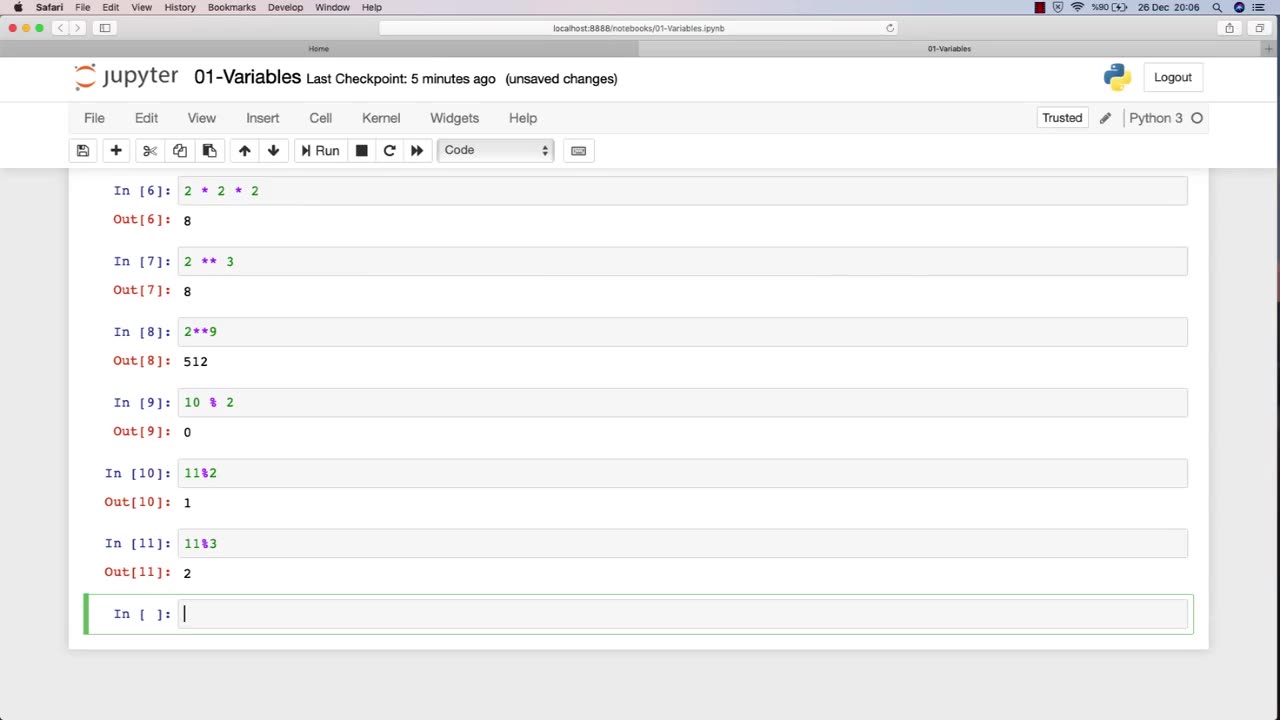
Chapter-27, LEC-2 | Numbers | #ethicalhacking #hacking #education #cybersport #cybersecurity
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram
Ethical hacking is a field that involves the use of various techniques and tools to identify and address vulnerabilities in computer systems and networks. Numbers play a critical role in ethical hacking, and understanding how to work with numbers is essential for success in this field.
Here are some examples of how numbers are used in ethical hacking:
IP Addresses: IP addresses are used to identify network devices and are essential for ethical hackers to understand. Ethical hackers use IP addresses to scan for open ports, identify potential vulnerabilities, and carry out attacks.
Ports: Ports are used to establish connections between devices on a network. Ethical hackers use knowledge of port numbers to scan for vulnerabilities, carry out attacks, and test the security of a network.
Passwords: Passwords are often used to protect sensitive information in computer systems and networks. Ethical hackers use various techniques to crack passwords, such as brute-force attacks, dictionary attacks, and rainbow table attacks.
Encryption: Encryption is the process of converting data into a secure format that cannot be read by unauthorized parties. Ethical hackers use their understanding of encryption algorithms and techniques to identify vulnerabilities and weaknesses in encryption systems.
Binary and hexadecimal: Binary and hexadecimal are number systems used in computing. Ethical hackers use their understanding of these number systems to analyze and manipulate data at the low-level, such as reverse engineering software or discovering vulnerabilities in firmware.
Overall, a strong understanding of numbers is essential for success in ethical hacking. By understanding how numbers are used in this field, ethical hackers can more effectively identify and address vulnerabilities in computer systems and networks.
-
 LIVE
LIVE
tminnzy
15 minutes agoSmooth Moves Only 💨 | Naraka: Bladepoint Chill Gameplay | !gx | !rumble
111 watching -
 1:04:33
1:04:33
BonginoReport
2 hours agoWill The LA Dodgers Dodge WH Visit?! - Nightly Scroll w/ Hayley Caronia (Ep.172) - 11/06/2025
9.94K25 -
 LIVE
LIVE
Tundra Tactical
3 hours agoDadlefield Game Night BF6 New Update Weapon Grind
98 watching -
 15:39
15:39
Megyn Kelly
3 hours agoTucker Carlson on Why He Interviewed Nick Fuentes and What He Wanted to Convey To Him
23.9K43 -
 1:14:10
1:14:10
Kim Iversen
3 hours agoZionists PANIC Over Muslim Mayor In NYC
57.9K82 -
 1:50:40
1:50:40
Redacted News
3 hours agoBREAKING! Trump Makes HUGE Announcement Trying To Save MAGA, Cost of Living & Israel CRUSHED GOP
91.8K160 -
 LIVE
LIVE
Dr Disrespect
9 hours ago🔴LIVE - DR DISRESPECT - ARC RAIDERS - QUEST MASTER
1,462 watching -
 2:17:37
2:17:37
The Quartering
5 hours agoFooled Again! Mamdani Backtracks Everything & Today's Breaking News!
187K107 -
 1:17:04
1:17:04
DeVory Darkins
6 hours agoPelosi SURRENDERS announces retirement and Bernie Sanders makes stunning admission
108K111 -
 4:35:22
4:35:22
StoneMountain64
6 hours agoArc Raiders is actually INCREDIBLE
62.3K2