Premium Only Content

Chapter-18 , LEC-1 | Hacker Methodology Introduction | #ethicalhacking #youtube #cybersport
Hacker methodology refers to the process and techniques used by hackers to gain unauthorized access to computer systems, networks, or data. Understanding hacker methodology is essential for developing effective security measures to prevent and detect cyberattacks.
The first step in hacker methodology is reconnaissance, or gathering information about the target system or network. This may involve scanning for open ports or vulnerabilities, researching the organization and its employees, or social engineering to obtain login credentials.
Once reconnaissance is complete, the hacker will attempt to gain access to the target system or network. This may involve exploiting a vulnerability in the software or network configuration, using stolen login credentials, or launching a phishing attack to trick users into revealing sensitive information.
Once access has been gained, the hacker will often establish a backdoor, or a method of maintaining access to the system even after the initial attack has been detected and blocked. This may involve installing malware, creating a new user account with elevated privileges, or modifying system files to hide their presence.
Once the backdoor has been established, the hacker may use the compromised system to launch further attacks or steal sensitive data. This may involve installing additional malware to capture keystrokes or screen captures, or using the compromised system as a launching point for attacks on other systems or networks.
Finally, the hacker will attempt to cover their tracks and erase evidence of the attack. This may involve deleting logs or modifying system files to hide their activity, or launching a denial-of-service attack to disrupt system operations and distract security teams.
Overall, understanding hacker methodology is essential for developing effective security measures to prevent and detect cyberattacks. By identifying and addressing vulnerabilities in the system or network, implementing strong access controls and monitoring measures, and regularly reviewing and updating security protocols, organizations can better protect themselves from the threats posed by hackers.
-
 4:33:50
4:33:50
Right Side Broadcasting Network
21 hours agoLIVE REPLAY: President Trump Holds a Press Conference with Prime Minister Keir Starmer - 9/18/25
52.8K38 -
 1:01:35
1:01:35
The Rubin Report
3 hours agoJimmy Kimmel Humiliated as NY Post Exposes His Dark Reaction to Being Canceled
49.2K88 -
 12:49
12:49
Clownfish TV
9 hours agoJimmy Kimmel Pulled OFF THE AIR for Charlie Kirk Comments?! | Clownfish TV
5.42K19 -

TheAlecLaceShow
2 hours agoJimmy Kimmel FIRED | ANTIFA Labeled Terrorist Org | Guest: Matt Palumbo | The Alec Lace Show
3.82K4 -
 1:44:57
1:44:57
Steven Crowder
5 hours ago🔴 FAFO: Jimmy Kimmel's gets Chopped & The Left is Freaking Out
446K335 -
 1:01:44
1:01:44
VINCE
5 hours agoThe "Finding Out" Phase Has Officially Begun | Episode 128 - 09/18/25
267K315 -
 DVR
DVR
The Shannon Joy Show
3 hours ago🔥🔥Jimmy Kimmel Canned For Charlie Kirk WrongSpeak - MAGA Cheers🔥🔥
19.8K20 -
 1:46:01
1:46:01
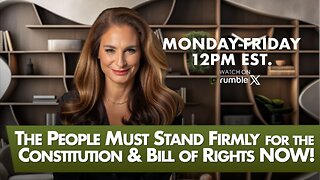
The Mel K Show
2 hours agoMORNINGS WITH MEL K The People Must Stand Firmly for the Constitution & Bill of Rights NOW 9-18-25
25.2K9 -
 29:39
29:39
Rethinking the Dollar
3 hours agoIntel & Nvidia Deal = Market Rigged? (You're Being Played)| Morning Check-In: Let's Talk...
12.2K -
 1:00:41
1:00:41
Trumpet Daily
2 hours ago $1.25 earnedTrumpet Daily LIVE | Sept. 18, 2025
26.2K2