Premium Only Content
This video is only available to Rumble Premium subscribers. Subscribe to
enjoy exclusive content and ad-free viewing.
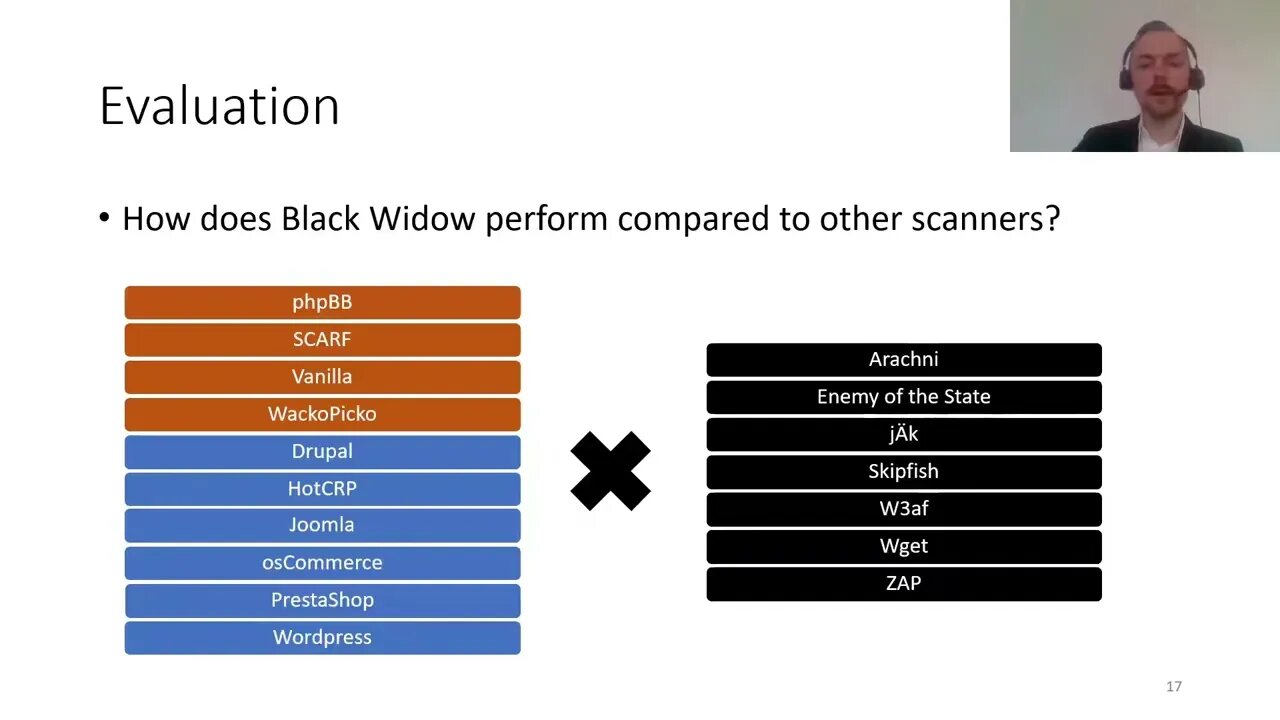
Black Widow Blackbox Data driven Web Scanning
Loading comments...
-
 1:33:14
1:33:14
Roseanne Barr
2 hours agoGod's Sting Operation | The Roseanne Barr Podcast #123
90.1K43 -
 LIVE
LIVE
Kim Iversen
1 hour agoWHAT?! Epstein Emails Claim Trump Did THIS To Bill Clinton...
1,353 watching -
 LIVE
LIVE
EricJohnPizzaArtist
1 hour agoAwesome Sauce PIZZA ART LIVE: SKANKFEST DAY ONE!
288 watching -
 DVR
DVR
vivafrei
8 hours agoAn Inconvenient Study: Live with Del Bigtree! FBI "Fast Response" Fact Checked! Megyn Kelly & MORE!
76.1K30 -
 1:35:03
1:35:03
Russell Brand
3 hours agoDemocrats Drop Epstein Emails — All About Trump - SF650
65K31 -
 LIVE
LIVE
Nerdrotic
2 hours agoBBC Crashout | Hollywood For Sale | Battle of the Blonde's | Witcher BOMBS - Friday Night Tights 380
1,320 watching -
 14:26
14:26
Upper Echelon Gamers
3 hours ago $0.13 earnedThe Carvana Scam - A Predatory BUBBLE
3.66K3 -
 LIVE
LIVE
LFA TV
20 hours agoLIVE & BREAKING NEWS! | FRIDAY 11/14/25
1,059 watching -
 LIVE
LIVE
Dr Disrespect
6 hours ago🔴LIVE - DR DISRESPECT - BLACK OPS 7 - LAUNCH DAY CHAMPION
1,167 watching -
 DVR
DVR
StoneMountain64
4 hours agoCall of Duty Black Ops 7 Gameplay LAUNCH DAY
34.8K