Premium Only Content
This video is only available to Rumble Premium subscribers. Subscribe to
enjoy exclusive content and ad-free viewing.
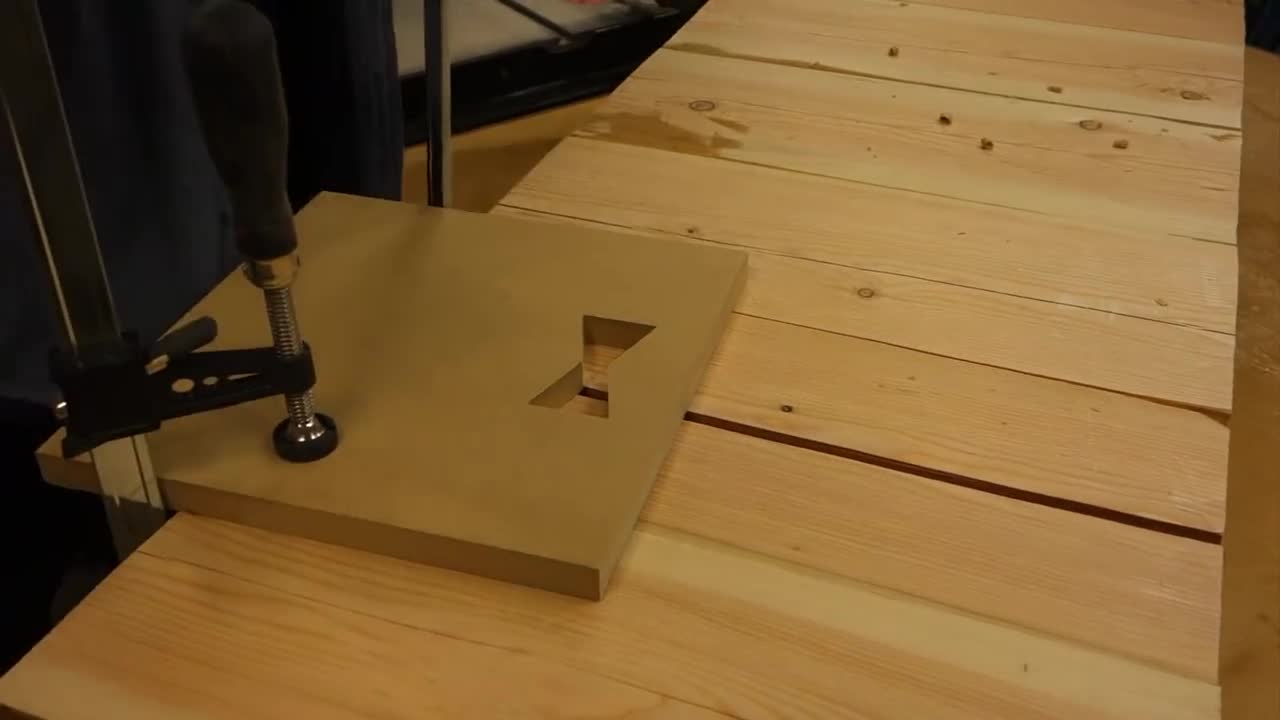
nd asymmetric cryptosystems
2 years ago
8
lacement of certificates and key pairs
Cross authentication, separation of encryption key and signature key; Support non repudiation of digital signature; Key history management and other functions. Using digital signature can confirm two points: first, the information is sent by the signer; Second, the information has not been modified since it was issued until it was received. A perfect signature mechanism should reflect the sending par
Loading comments...
-
 LIVE
LIVE
The Big Mig™
4 hours agoBiden Has Terminal Cancer
3,263 watching -
 LIVE
LIVE
LFA TV
17 hours agoLFA TV LIVE STREAM - MONDAY 5/19/25
8,299 watching -
 LIVE
LIVE
Caleb Hammer
1 hour agoHe Came Here To Fight Me | Financial Audit
191 watching -
 LIVE
LIVE
Wendy Bell Radio
6 hours agoThe Big Lie
10,066 watching -
 LIVE
LIVE
Discover Crypto
1 hour agoEMERGENCY BITCOIN ALERT! Bond Market Crisis Will Fuel MASSIVE Pump!
219 watching -
 LIVE
LIVE
Major League Fishing
4 days agoLIVE! - Bass Pro Tour: Heavy Hitters - Day 3
295 watching -
 1:08:03
1:08:03
Dear America
3 hours agoJOE BIDEN HAS CANCER!! When did they know and how long have been hiding it…
158K55 -
 LIVE
LIVE
Badlands Media
4 hours agoBadlands Daily: May 19, 2025
5,218 watching -
 48:11
48:11
Randi Hipper
1 hour agoBITCOIN ALL TIME HIGH COMING!! PRICE ACTION EXPLAINED
4.41K1 -
 49:58
49:58
The White House
2 hours agoPress Secretary Karoline Leavitt Briefs Members of the Media, May 19, 2025
30.8K15