Premium Only Content
This video is only available to Rumble Premium subscribers. Subscribe to
enjoy exclusive content and ad-free viewing.

2FA (Crypto.com Breach) Is Safe - If It's Implemented Correctly. Your Cell Phone Is The Problem
3 years ago
1
By which we aren't blaming you, we're blaming your technology.
IN this snippet from the podcast, we deep dive on alternative ways that 2FA could (and ideally should) have been implemented to help protect people. Nothing is a sure bet, but it's better than what we have.
In summary: As long as a cell phone is in the mix, there's a risk - thus why we never supported Crypto.com's "mobile only" development strategy.
Music: “Meadow Call” by Jan-Michael Hökenschnieder & Fachhochschule Dortmund, licensed under Creative Commons Attribution 4.0 International (CC BY 4.0).
Loading comments...
-
 2:36
2:36
KTNV
3 years agoHow to save on your cell phone plan
18 -
 2:11:25
2:11:25
Nikko Ortiz
2 hours agoLATE NIGHT GAMING... | Rumble LIVE
69.7K6 -

Dr Disrespect
10 hours ago🔴LIVE - DR DISRESPECT - ARC RAIDERS - NORTH LINE UPDATE
112K8 -
 LIVE
LIVE
PNW_Guerrilla
2 hours agoHalo CE
175 watching -
 1:01:11
1:01:11
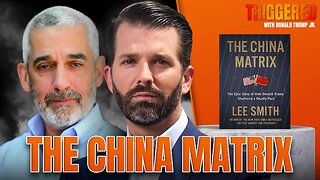
Donald Trump Jr.
7 hours agoThe China Matrix with Journalist Lee Smith | TRIGGERED Ep.291
79.4K70 -
 LIVE
LIVE
XDDX_HiTower
48 minutes agoARC RAIDERS, FIRST DROP IN
44 watching -
 59:22
59:22
BonginoReport
4 hours agoWH Trolls Dems After Government Reopens - Nightly Scroll w/ Hayley Caronia (Ep.177)
54.5K37 -
 LIVE
LIVE
Spartan
4 hours agoFinishing Nine Sols, Another game after. Some College Halo Matches later on as well
38 watching -
 LIVE
LIVE
JDubGameN
1 hour agoI'm a raider | Road to LootFest 2026 | DubNation LIVE
41 watching -
 LIVE
LIVE
Mally_Mouse
3 days ago🎮 Throwback Thursday! Let's Play: Stardew Valley pt. 32
99 watching